I just arrived at my hotel after a long day in the studio at the Microsoft headquarters here in Stockholm. Me and my colleagues at Altitude 365 produced a live broadcast in Swedish today, about Microsoft cloud security, and I rounded up the day talking about Windows Autopilot and how to get to a modern and more secure desktop with Windows 10.
We had a lot of fun and I hope people learned something new from our event. We’re going to post the videos online in a couple of days so keep an eye on the Altitude 365 website if you missed the event today.
I will blog about Autopilot in the upcoming weeks but today I would like to share a troubleshooting tip in Conditional Access that I had to use when I prepared for my Autopilot session and couldn’t log in to Azure AD during the Windows 10 installation. Conditional Access blocked the authentication and I had to find out why.
The Issue
Sometimes when you try to logon a Conditional Access protected tenant you get the CA error page telling you that you can’t get there from here. Here are a couple of examples:
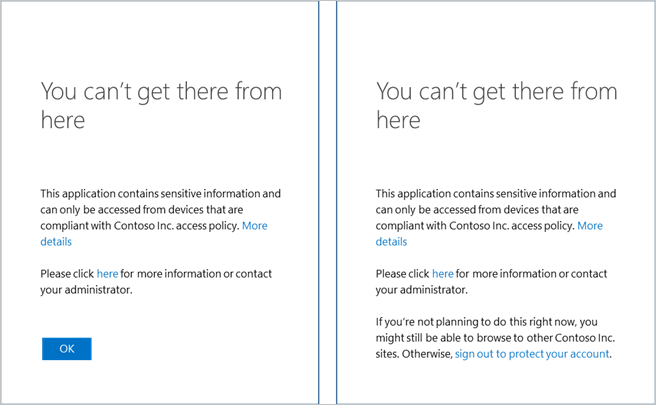
You might understand from the text, what the issue is but in some cases it’s more ambiguous and the administrator will need to dig a little deeper to understand what CA policy is blocking the authentication.
Well, I have good news for you. This information is logged in the Azure AD Sign-In log.
Conditional Access in the Azure AD Sign-In Log
Go to the Azure portal and the Azure AD blade. Click on Sign-ins. Here you can filter sign-ins on Conditional Access status and you can see if CA was used and if the authentication was granted or if it failed.
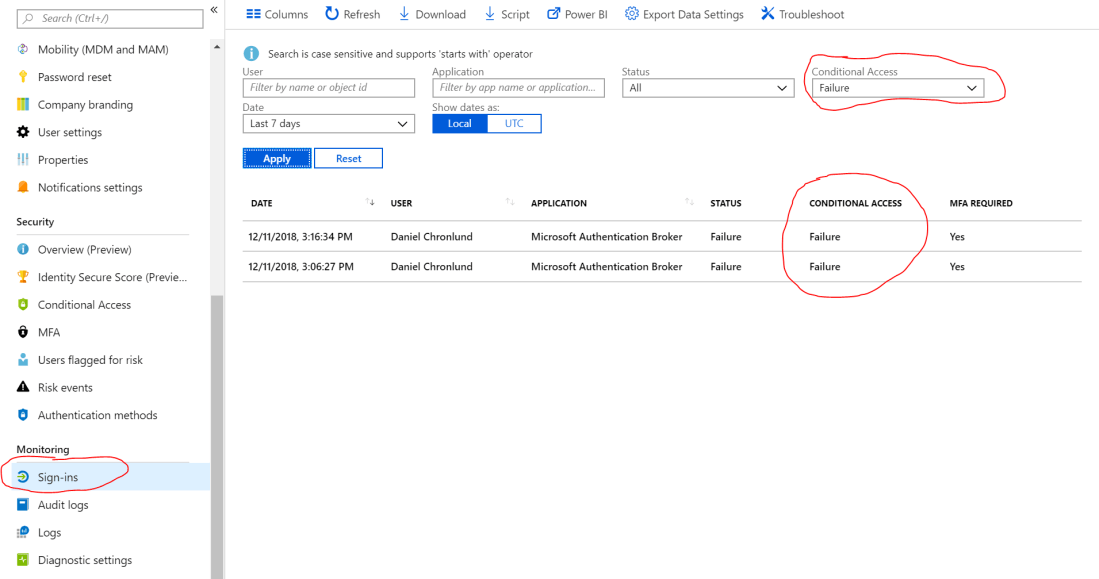
If you click on a sign-in you get additional information about the attempt. On the Basic info tab you can see the failure reason and it most often clearly explains why the authentication was denied. In this case, CA required a domain joined device and therefor failed since I tried to authenticate from a new device.
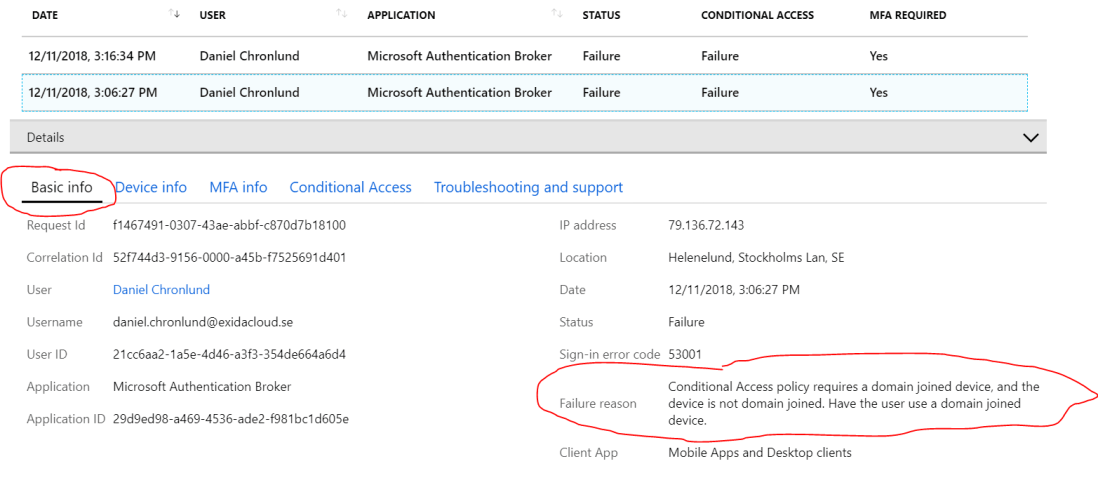
You can get additional details on the Conditional Access tab. Here you see the evaluation of each individual CA policy and which ones failed and what the Grant Controls for that policy were. In this case we see the Require domain-joined device.
We also see Terms of use since I never got a chance to read and accept those.

I hope this little troubleshooting tip will help you when CA is giving you a hard time.
Please follow me here, on LinkedIn and on Twitter!
One thought on “Conditional Access Logs in Azure AD”