In a Microsoft zero trust architecture, Azure AD Conditional Access is the guard and policy enforcer for our kingdom. Almost every customer I meet with has implemented Conditional Access in one way or another. Have a look at my Conditional Access policy design baseline if you need help getting started. Conditional Access is what sits between the user/device authenticating, and the service/resource in our cloud (or hybid cloud). For that reason, Conditional Access needs to be carefully monitored and you need to act on any configuration mistakes, insecure configuration changes, and policy disablements.
Microsoft Sentinel is our SIEM solution in the Microsoft cloud and it now includes a very handy export/import feature of analytic rules (Sentinel alert rules) using JSON. It work’s really well and the best thing about it is that it is tenant independent, meening that the exported rules can be imported in any tenant with the same result. A while back I decided to create a Conditional Access rules pack for Sentinel. I decided to simpy call it Conditional Access Sentinel Analytics Rules Pack, and here it is!!

I have published the source JSON on GitHub and will also keep this blog post updated whenever I release a new version. My goal is to provide new versions as new Conditional Access features are released and whenever I learn something new worth to include.
Current Version
| Current Version | 1 |
| Released | 2022-04-13 |
| Analytics Rule Name | Severity |
| Conditional Access – A Conditional Access app exclusion has changed | Low |
| Conditional Access – A Conditional Access Device platforms condition has changed (the Device platforms condition can be spoofed) | Low |
| Conditional Access – A Conditional Access policy was deleted | Low |
| Conditional Access – A Conditional Access policy was disabled | Low |
| Conditional Access – A Conditional Access policy was put into report-only mode | Low |
| Conditional Access – A Conditional Access user/group/role exclusion has changed | Low |
| Conditional Access – A Conditional Access policy was updated | Informational |
| Conditional Access – A new Conditional Access policy was created | Informational |
Note: These analytic rules automatically creates alerts in Sentinel, and incindent creataion is also enabled. Related alerts created within an hour are grouped togehter in the same incident for your convinience.
Download the Conditional Access Sentinel Analytics Rules Pack
You can get the latest version on GitHub.
Installation
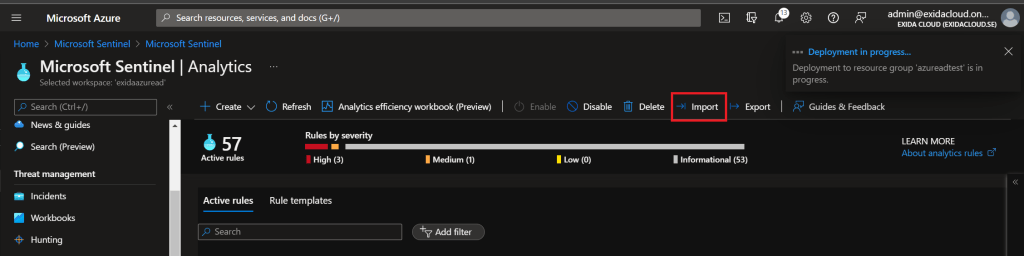
Simply import the JSON file in Sentinel under Analytics. Click on Import and select the downloaded JSON file on your computer. The deployment is quick and the rules are enabled automatically. All done!
Update Rules
To update to the latest version of the Conditional Access Sentinel Analytics Rules Pack, just download the latest version and import it again. Sentinel will automatically replace the existing analytic rules (based on their name) with the new versions.
Investigate Alerts
Each rule is generated by a Kusto query that includes some additional details about the alert. First, open the incident and click on the relevant alert in the Timeline. Click on the Link to LA to see the acctual query result containing the details.

In this case, we can see the details of the alert A Conditional Access policy was disabled. The state was changed from enabled to disabled. Easy!

Summary
It’s important to keep a close eye on your Conditional Access policies. They are the zero trust policy enforcer for your environment and if any of them are disabled or missconfigured, that could meen free access for adversaries. I hope you find this Sentinel analytics rules pack usefull.
Please follow me here, on LinkedIn and on Twitter!
This is awesome. Much appreciated. It seems like the alerts don’t have much information though. For instance, I created a new CA policy and the alert/incident does not elaborate or tell me anything about what happened…other than…it happened. Is there a way to get some more meat into the incidents/alerts?
All details are included. Click on the event in the alert and you’ll get the full details.