Cyber security is a complex topic and today’s threat actors and security threats are highly sophisticated. Security must be implemented in multiple layers to make it hard for the threat actors to succeed. In many cases security success comes from being the most “expensive” target. Attackers are in it for the money and they go where their time and effort pays the most. Simply put, if you raise the bar high enough, the bad guys will go somewhere else.
I’ve been thinking about different security strategies lately and I’ve asked myself if there is a golden approach to M365 security. My conclusion is that we need to apply a layered approach to Microsoft 365 security, and that there are four major layers of Microsoft 365 security that every organisation must put energy into. In this blog post I explain my four-layered approach to working with security in Microsoft 365, aka “The Microsoft 365 Security Onion”.
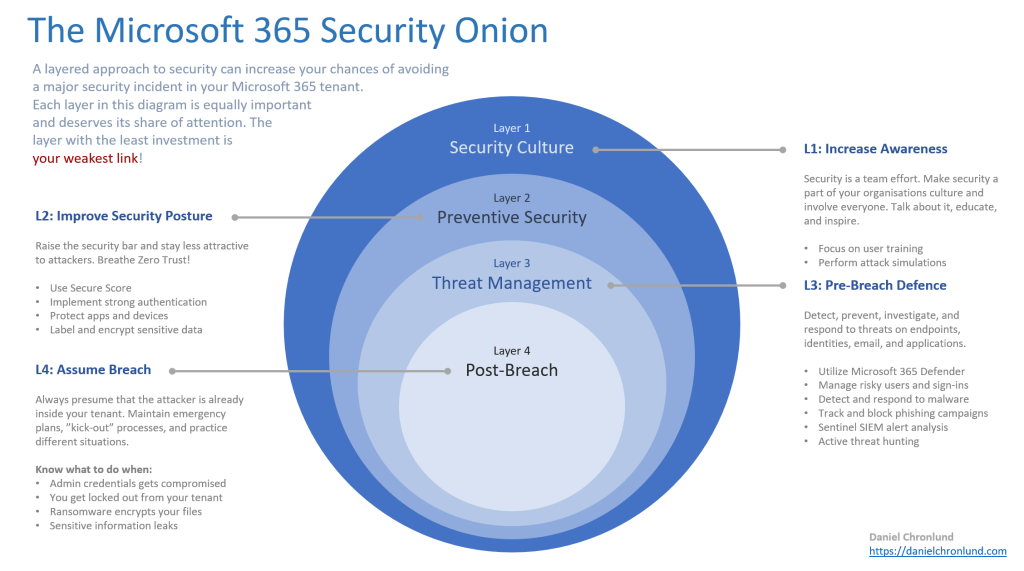
Feel free to use the above diagram in your own strategical presentations if you find it useful. The idea is to visualise four key areas that we need to work with, from security culture, preventive security, threat management, to post-breach management. I will try to explain why each area is important and why you shouldn’t ignore it.
Layer 1 – Security Culture
Our first layer is an important, but unfortunately often forgotten security layer, namely the overall security culture of the organisation. The weakest link of many organisations are their users. Security is a team sport and all employees, partners, and other users must contribute by staying aware and taking care of organisation data and resources. If we can build a security culture where everyone is well trained, understands our threats, and are always on their toes when handling email, files, and company data, then we are much better equipped against attacks like phishing, credential theft, and social engineering. This is super important!
Regularly train users and inform them on current threats and encourage them to stay alert. Remind them and share security information and statistics on a regular basis. Perform attack simulation against your organisation and put extra training efforts on those individuals more susceptible to attacks. By doing this, we can stop many attacks before they even start.
Layer 2 – Preventive Security
Our second layer is about increasing our security posture by implementing a zero trust security model. We use Secure Score to implement security recommendations and to make different cyber attacks harder or impossible to perform against our tenant. Conditional Access is critical in this layer and we want to bring in as many security signals as possible into the policy engine. This means that we want to enable integrations with other M365 services like Azure AD Identity Protection, Defender for Endpoint, Intune, and Microsoft Cloud App Security. The more the merrier!
Additional security signals means more accurate access decisions based on the current scenario. The policy engine can automatically block access if anything seams suspicious on the user level or on the device level. The engine can also act based on what happen after authentication, during the ongoing session.
We should go through tenant security settings like guest access configuration, Teams security configuration, device registration configuration, etc. A new Microsoft 365 tenant is very “everything is default on” but this is often not the way we want it configured. There are some settings, especially regarding what guests can do and see, that we do want to change in most cases. Again, Secure Score is a great guide to many of these settings. Also, the Microsoft 365 Defender Threat Analytics is a powerful tools to understand what threat Microsoft security teams sees and learns about and how they affect our organisation. This is a tool that you should use to prevent attacks!
Layer 3 – Threat Management
Our third layer is about monitoring and reacting on everything that happens in our tenant. We call this threat management and response and this is where your SOC lives. We need to have good alert rules in place for identities, devices, threat detection, and incidents. There are many different security products in play here but Microsoft 365 Defender makes it really easy to mange the tenant as a whole. I highly recommend investing in M365 Defender since it looks at alerts from all security products in Microsoft 365 and displays them in one central dashboard, creating unified incidents and incident reports. Your SOC can work with M365 security from one dashboard and respond to threats and alerts in a holistic way.
Automation is key in this layer and Microsoft Sentinel is also an important peace in this puzzle. We can create intelligent queries to find threats across our cloud and other services and we can understand what’s happening on a completely different level. We can automate the response and act accordingly, making it easier to handle the huge amount of security signals any organisation is exposed to these days.
But my most important advice is to make sure you have the proper processen in place. All the security tools in the world won’t do you any good if you don’t act on alerts and incidents.
Layer 4 – Post-Breach
In a zero trust model we assume breach. In our fourth layer we presume that the attacker is already on the inside and we need to know what to do under different circumstances. We need to have a plan and process for attacker account clean-up, aka “kick-out” process. We need to know how to respond to a successful ransomware attack, where our files gets encrypted. I believe that many organisations don’t have this in place. We spend a lot of time and energy to protect the organisation against cyber attacks, but we lack a basic understanding in what we need to do when things go wrong, because they will!
I’ve recently blogged about what you can do when your Azure AD gets compromised. This is a good start but there are more things you need to do. Know how to shut down affected services, restore different kinds of back-ups, how you open support tickets with Microsoft, who you can contact if you need expert advice during an incident, etc. With thorough preparations you can minimise downtime and damage.
Summary
By managing these four layers as individual areas that all needs attention, you can increase your security posture in Microsoft 365. Of course, this approach is probably applicable to other services and scenarios as well. Anyway, I believe that a solid security culture, preventive security, great threat and incident management, and an assume breach methodology, will help you in your security work. I hope that this blog post inspires you to find your weakest link and to create a plan to further balance and improve your security posture.
Please follow me here, on LinkedIn and on Twitter!
Amazing article! Loved every piece of it. Stumbled upon this yesterday and the diagram is going to be of great use. I am designing a similar layered security using defense in depth but for Cloud Workloads.
Thank you! Glad you find it useful 😊