Exchange Online, part of Office 365, is one of the most popular email services in the world. It’s used by everything from huge enterprises to small one-man businesses. It’s not unexpected that it is one of the most popular tagets for spam and phishing attacks. In this article I will explain how you can improve your organisations email reputation on the Internet with Exchange Online and some PowerShell.

About SPF, DKIM and DMARC
There are three different technologies that are used to secure an organisation’s email domains (SMTP domains) and in that way contribute to a good email reputation on the Internet. Different DNS records are used by the receiving email server to determine whether incoming emails are legitimate or not.
Most organisations already use the Sender Policy Framework (SPF), which basically is a list of valid mail servers and services that can send email using the mail domain in question. SPF has shortcomings and is not adequate protection. This is where DKIM and DMARC comes into the picture.
DKIM – DomainKeys Identified Mail – Like SPF but uses cryptography to determine that the sending server is allowed to send email using the SMTP domain. All outgoing emails are digitally signed with a private key. The receiving server can then use the public key to determine whether the emails are coming from the correct server or not. The public key is saved in Office 365 and the recipient finds them through DNS (CNAME and TXT records). DKIM is enabled per SMTP domain.
DMARC – Domain Message Authentication Reporting & Conformance – Works much like SPF where there is a DNS record that contains all allowed email servers for a specific SMTP domain, but there is an important difference. With DMARC, sender and receiver will co-operate and share information about how their different email systems work and how they see each other’s incoming emails. The receiver sends DMARC reports to the sender which the sender can analyse. The sender recommends whether the recipient should refuse, quarantine suspicious email or just report back to the sender that the email failed in the receivers DMARC control. DMARC reports are sent back to a specified mailbox. DMARC is enabled for each SMTP domain.
PowerShell Tips and Tricks for SPF, DKIM and DMARC in Exchange Online
You will probably want to enable these protection technologies for all your SMTP domains that can be used for sending email from your organisation. Remember to include domains that you mainly use, or can use, with SMTP relaying and such. This PowerShell command will fetch all your SMTP domains actually used in mailboxes in Exchange Online. The result will be put in $Domains that we use in later commands.
# Get all SMTP domains actually used in Exchange Online.
$Domains = Get-Mailbox -ResultSize Unlimited | Select-Object EmailAddresses -ExpandProperty EmailAddresses | Where-Object { $_ -like "smtp*"} | ForEach-Object { ($_ -split "@")[1] } | Sort-Object -Unique
$Domains
If you prefer to manually select domains, simply add them like this instead.
# Manually add domains to manage. $Domains = "example1.com", "example2.com"
You can verify DNS records for SPF, DKIM and DMARC with this PowerShell script. It will create a simple text and send it to your clipboard, containing all records available for the SMTP domains in $Domains.
# Verify DKIM and DMARC records.
Write-Output "-------- DKIM and DMARC DNS Records Report --------"
Write-Output ""
$Result = foreach ($Domain in $Domains) {
Write-Output "---------------------- $Domain ----------------------"
Write-Output "DKIM Selector 1 CNAME Record:"
nslookup -q=cname selector1._domainkey.$Domain | Select-String "canonical name"
Write-Output ""
Write-Output "DKIM Selector 2 CNAME Record:"
nslookup -q=cname selector2._domainkey.$Domain | Select-String "canonical name"
Write-Output ""
Write-Output "DMARC TXT Record:"
(nslookup -q=txt _dmarc.$Domain | Select-String "DMARC1") -replace "`t", ""
Write-Output ""
Write-Output "SPF TXT Record:"
(nslookup -q=txt $Domain | Select-String "spf1") -replace "`t", ""
Write-Output "-----------------------------------------------------"
Write-Output ""
Write-Output ""
}
$Result | Clip
Example of output where the domains has no records:

Example of output where the domains HAS records:

Based on your findings with the above script, you need to add additional DNS records. This PowerShell script will help you create an order for your DNS team. Make sure you change $TenantName and $ReportMailbox.
# Create order text for DKIM and DMARC records.
$TenantName = "example.onmicrosoft.com"
$ReportMailbox = "dmarcreports@example.com"
$Result = "Protection`tDomain`tTyp`tHost name`tValue`tTTL`n"
foreach ($Domain in $Domains) {
$Result += "SPF`t$Domain`tTXT`t@`tv=spf1 include:spf.protection.outlook.com -all`t3600`n"
$Result += "DKIM`t$Domain`tCNAME`tselector1._domainkey`tselector1-$($Domain -replace "\.", "-")._domainkey.$TenantName`t3600`n"
$Result += "DKIM`t$Domain`tCNAME`tselector2._domainkey`tselector2-$($Domain -replace "\.", "-")._domainkey.$TenantName`t3600`n"
$Result += "DMARC`t$Domain`tTXT`t_dmarc`tv=DMARC1; p=none; pct=100; rua=mailto:$ReportMailbox; ruf=mailto:$ReportMailbox; fo=1`t3600`n"
}
$Result | Clip
The script will create an tab separated order text and send it to your clipboard. This text can be pasted right into Excel for further formating.
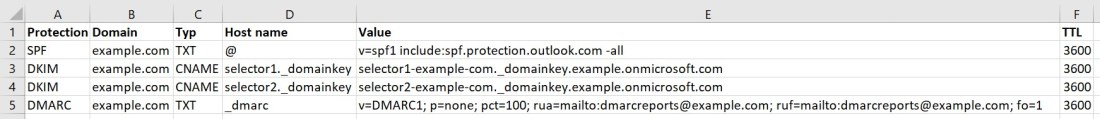
These are all the DNS records needed for SPF, DKIM and DMARC in Exchange Online. Send it to your DNS team. Note that the DMARC record will put your SMTP domain in monitoring mode. This will make receivers send you DMARC reports but they won’t block your emails if the DMARC check fails.
You should evaluate the results some time before switching the mode to enforce which will cause the receiver to block emails failing the DMARC check.
SPF and DMARC will automatically start to work in Exchange Online. DKIM needs to be enabled for each domain after you’ve added the DNS records. Here are three nice PowerShell scripts you can use to list and activate DKIM in Exchange Online for your domains.
# Get list of existing DKIM configs (using Exchange Online PowerShell). Get-DkimSigningConfig
# Enable new DKIM (using Exchange Online PowerShell).
foreach ($Domain in $Domains) {
Write-Verbose -Verbose -Message "Enabling DKIM for $Domain..."
New-DkimSigningConfig -DomainName $Domain -Enabled $true
}
# Set existing DKIM (using Exchange Online PowerShell).
foreach ($Domain in $Domains) {
Write-Verbose -Verbose -Message "Enabling DKIM for $Domain..."
Set-DkimSigningConfig -Identity $Domain -Enabled $true
}
I hope that these PowerShell tips will speed up your SPF, DKIM and DMARC deployments. It sure has for me.
Please follow me here, on LinkedIn and on Twitter!
Great article! But what if your results are:
*** Request to UnKnown timed-out
Non-authoritative answer:
Thank you! You can probably ignore those DNS errors. Focus on the result sent to clipboard. If the result for a lookup is empty, then you are missing SPF, DKIM or DMARC.
Great article! I’ve added nslookup in an try catch and even added ErrorAction SilentlyContinue however any errors are still written e.g. Non-existene domain. Any ideas?