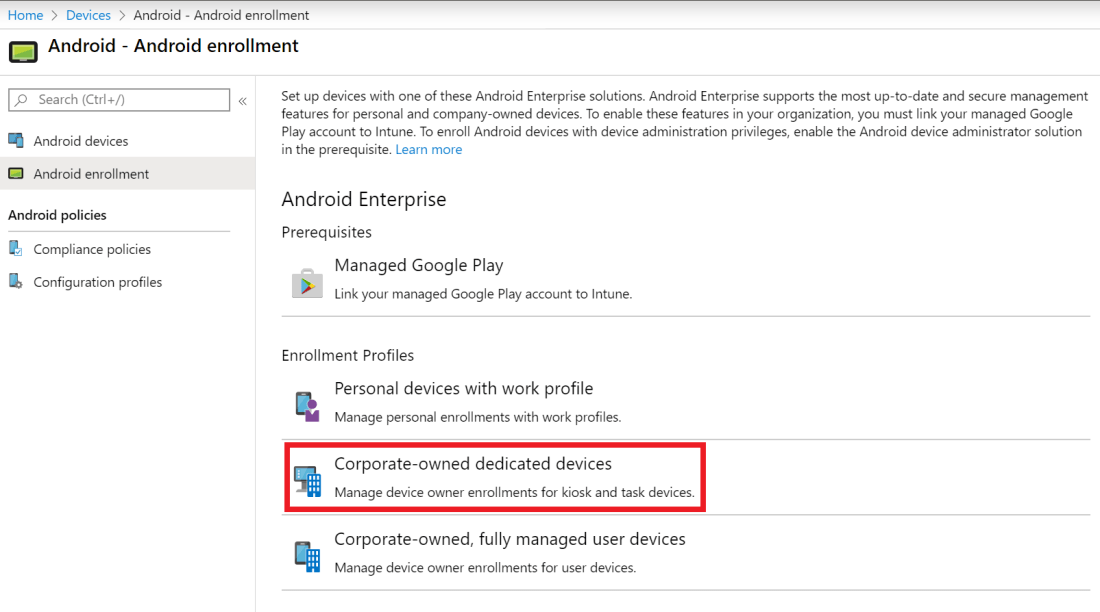
If you’re enrolling Android Enterprise corporate-owned dedicated devices (kiosk devices) using Microsoft Endpoint Manager (or any other MDM service) you might be familiar with the fact that the Android enrollment token generated by Google has a maximum lifetime of 90 days. That’s how far in to the future you can set the expiration date. This means that you are required to renew the token at least that often.

Of course, this manual way of work is a waste of time, easily forgotten and won’t provide any real business value. But we’re in luck because Microsoft provides us with tools to automatically renew Android enrollment tokens via Microsoft Graph and PowerShell.
Remember that the token goes hand in hand with its QR code so when you renew the token the QR code will change and you need to use the new one when enrolling new devices. No worries, this will not affect existing devices enrolled with the old token.
Let’s dig into the details. If you’re interested, you can find the Microsoft Graph endpoint documentation here.
Your Azure AD application requires the following Microsoft Graph permissions to renew tokens: DeviceManagementConfiguration.ReadWrite.All
Note that, as of writing (February 26th, 2020), this is a beta endpoint, not well documented, and a bit buggy. Even though the documentation states that Graph application permissions are sufficient to renew the token, you will actually need to use delegated permissions and sign in with an Intune admin. Trust me, I learned this the hard way.
First you need to connect to Microsoft Graph as an Intune Admin. If you’re new to this in PowerShell, you can find the functions I use in this blog post. You can also find general info about registering an Azure AD app and grant it Microsoft Graph permissions here.
When you’ve loaded the PowerShell functions mentioned above. Connect and authenticate to Microsoft Graph like this (you will get prompted to sign in with your Intune admin account). Remember to change the client ID and client secret accordingly.
# Connect to Microsoft Graph with delegated credentials. $ClientID = '' $ClientSecret = '' $AccessToken = Connect-MsGraphAsDelegated -TenantName $TenantName -ClientID $ClientID -ClientSecret $ClientSecret
Now, you can list all your Android Enterprise enrollment profiles like this:
# List Android enrollment profiles. $Uri = 'https://graph.microsoft.com/beta/deviceManagement/androidDeviceOwnerEnrollmentProfiles' Get-MsGraph -AccessToken $AccessToken -Uri $Uri
You can get the profile ID of a specific Android enrollment profile from it’s display name like this:
# Android enrollment profile display name.
$ProfileDisplayName = "Test"
# Get Android enrollment profile ID from displayName.
$Uri = 'https://graph.microsoft.com/beta/deviceManagement/androidDeviceOwnerEnrollmentProfiles'
$ProfileId = (Get-MsGraph -AccessToken $AccessToken -Uri $Uri | Where-Object { $_.displayName -eq $ProfileDisplayName}).id
$ProfileId
When you have the profile ID you can renew the token (including its QR code) like this:
# Renew token of selected Android enrollment profile (set expiration to 90 days (60*60*24*90=7776000 seconds)).
$Uri = "https://graph.microsoft.com/beta/deviceManagement/androidDeviceOwnerEnrollmentProfiles/$ProfileId/createToken"
$Body = @"
{
"tokenValidityInSeconds": 7776000
}
"@
Post-MsGraph -AccessToken $AccessToken -Uri $Uri -Body $Body
7776000 is 90 days in seconds and that’s the maximum value that Google allows for enrollment tokens for dedicated devices. You’ll get an error back if you try to set it longer.
You’ve now renewed the token and you can fetch the new token string like this:
# Get your Android enrollment profile token. $Uri = "https://graph.microsoft.com/beta/deviceManagement/androidDeviceOwnerEnrollmentProfiles/$ProfileId/?select=tokenValue" $EnrollmentToken = (Get-MsGraph -AccessToken $AccessToken -Uri $Uri).tokenValue $EnrollmentToken
Wonderful!!
Remember to distribute the new QR code if you’re using QR code enrollment (you can see it in the MEM portal). Also change the token in Android Zero-Touch, Samsung Knox Mobile Enrollment, etc if your’re using any of those services. I’m currently looking at automating this on the Google side as well.
I hope you find my experiences with dedicated device enrollment tokens helpful. Please follow me here, on LinkedIn and on Twitter!