The Fearsome Five is not only the name of a group of super villains from DC Comics. It is also a very suiting name for the top five cyber security threats to your organization in 2020. These five threats are not ranked and they are based on my own view of the security landscape with focus on the Microsoft cloud platform.
I regularly help organizations to recover from attacks and security issues related to these five cyber threats, and of course, also to prevent them from happening in the first place. No matter how big your organization is, you are affected by these threats and you need to deal with them. This blog post don’t have all the answers but its purpose is to help you focus on the right stuff. It’s difficult (if not impossible) to protect your organization from every threat out there but you need to try to make it as hard as possible for the bad guys to get to you.
That’s why it is very important that every one of these five threats gets your attention.
The Fearsome Five:
- Phishing Attacks
- Password Attacks
- Malware/Ransomware
- Data leakage and Shadow IT
- Unprotected mobile devices
Phishing Attacks
Phishing attacks is still one of the biggest threats to organizations. Massive amounts of emails are spammed against users with hope that some will open the provided links or attached files to give up their credentials or install malware.
The attacks are getting more sophisticated with some help from AI, translation services, and so on. Spear-phishing attacks are the most scary form of phishing since it’s targeted against specific organizations and even individuals.
You need to work with multiple layers of protection against this threat. The most important layer is to educate your users not to fall for these tricks in the first place. Thur-row security and IT hygien training for all employees will work wonders and protect your organization from phishing.
Of course, some users will fall in the trap anyway so you also need a sophisticated defense in the cloud service itself. There is built-in protection for known threats in Office 365 in form of Exchange Online Protection. But this is not enough since many threats are unknown, aka zero-day threats. This is where Office 365 Advanced Threat Protection takes over and analyses attachments and links by detonating them in sandboxes, called detonation chambers.
Office 365 ATP contains many other great security features like the Attack Simulator which can help you train your employees not to click on phishing email by simulating attacks against your own organization and measure its effectiveness and to find weak individuals.
Password Attacks
Identity attacks are almost always password based in some way. The traditional password attacks, like brute force attacks and password spray attacks, are trying to guess the users password. More common these days are the use of stolen accounts, like from a phishing attack for example, and you cannot protect your organization from these by implementing a strong password policy.
Instead the most important tools here are Multi-Factor Authentication and Conditional Access. MFA makes sure that your users must provide addition factors when authenticating and Conditional Access makes sure devices used are compliant with organization security standards, not too risky, not from an unsupported legacy protocol, etc.
Just by implementing MFA itself your organization is 99,9% better protected against password attacks.
Malware/Ransomware
Malware can find its way into your organization in many ways. Emails, links and shared documents are popular ways. No matter how they get in you need to have the right protection and emergency procedures in place because you will get infected at some point.
Ransomware is a form of malware which is rapidly growing in use. It’s a nasty type of malware since it will encrypt files and demand money to decrypt them.
To protect the organization from malware you need to tackle it from multiple angles. Office 365 ATP is important here as well and you can use the Treat Explorer to dig deep into how your organization is affected by malware. But you will also need a great endpoint protection and Windows Defender ATP can help you with that.
Microsoft Defender ATP, just like Office 365 ATP, will help you defend your organization from zero-day threats and both services are communicating with the Microsoft Intelligent Security Graph database to make sure that all Microsoft security products are aware of newly discovered threats.

Data Leakage and Shadow IT
Data leakage is often caused by unaware and unknowing users. Sensitive information gets emailed and shared publicly on the internet. Confidential organization information is stored in third-party cloud services, which is what we call Shadow IT. There are also regulations that the organization needs to follow, like the GDPR.
First of all, it is very important that the organization has a strict and clear data policy in place. This policy should explain how and where data must be stored. The policy should also describe how information should be classified.
When the policy is in place, it can be enforced by the tools in Office 365 and Microsoft Information Protection. Label information according to the organization data policy and apply protection and data loss prevention in the service.
Wouldn’t it be great if all confidential information just stayed where it belonged? Well, it’s possible in the Microsoft cloud.
For the Shadow IT part, Microsoft Cloud App Security is a great solution. It is a Cloud Access Security Broker (CASB) solution which is placed right between the user and the cloud service. This makes it possible to inspect the traffic and also enforce policys on it. You not just understand what unsanctioned cloud services your users use, you will also be able to help them protect organizational data by enforcing different kinds of policies.
Unprotected Mobile Devices
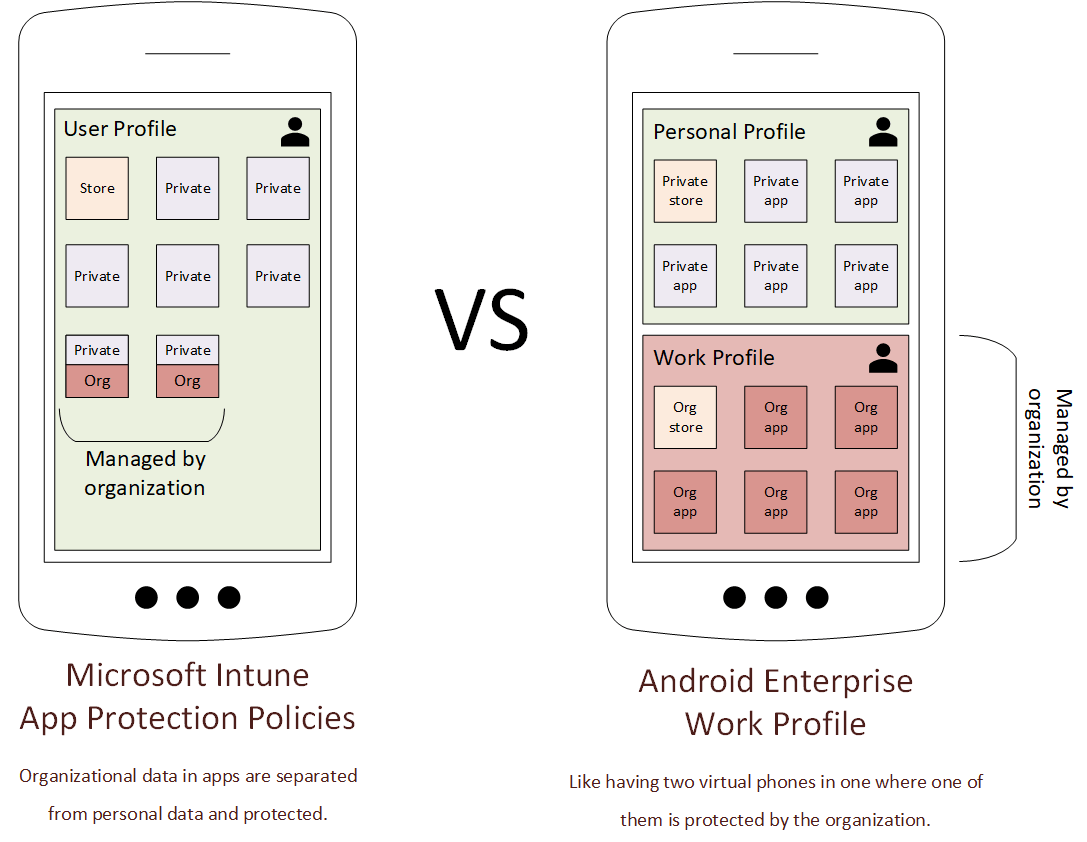
Last but not least, unprotected and unmanaged devices are a big security issue. Users bring sensitive data with them everywhere they go, on their work devices and on their personal devices. A stolen or lost device means lost data. A Mobile Device Management solution (MDM) is critical to make sure data stays protected and secure out there.
Microsoft Intune is the MDM solution integrated in the Microsoft cloud platform and it will help you protect organization data on managed and unmanaged devices (BYOD). Intune supports all mobile platforms including, iOS, Android and Windows and it is an important peace of the security puzzle since it will make sure devices follow organization security policy.
Summary
The Fearsome Five are real threats that all organizations must handle. User training and the right technical tools are critical for your success. This is a checklist of important stuff that you’ll need to tackle them:
- A clear security policy that all employees understand
- Continuous and relevant training for all users, both internal and external
- The right security products and license levels in place
- Monitoring with alerts
- An emergency plan
I hope this helps! Please follow me here, on LinkedIn and on Twitter.