It’s finally summertime and I’m writing the final part of this blog post from my newly installed hammock, sitting between two tall trees beside our weekend cottage. And it’s not a coincidence that I’m writing from a hammock because the message of this post is that you can save time with Azure Sentinel and do other stuff than manually monitoring logs in Microsoft 365.
I’ve been doing a lot of work around security in Microsoft 365 lately, helping customers to get a better overview of their logs and alerts. My goal is to provide easy to understand, custom made, dashboards for Azure Sentinel consolidating logs and alerts from all over Microsoft 365. This is a work in progress.
As you know, Microsoft 365 is a collection of products and services and they don’t all log to the same place or even in the same way. The table below shows some important places to keep an eye on. The table also gives you a hint if there is native Sentinel support, native Azure dashboard support and native email alert support for a particular service.
Please note that there are more logs which I haven’t listed here for now. Also, you most probably can integrate each and everyone of these services with Sentinel with some custom scripting/graph magic.
Microsoft 365 Logs and Alerts
Activate Azure AD Sign-ins Log Connector in Azure Sentinel
If you haven’t tried Sentinel yet, please do so right away!! It’s very easy to get started and activate the data connectors for Microsoft 365 mentioned in the table above. I will show you how to activate the Azure AD connectors here as an example.
Go to the Azure Portal and search for Sentinel under All services. Create a new Log Analytics workspace (which is the engine that drives Sentinel). Now, inside the Azure Sentinel blade, click on Data connectors and click Configure under Azure Active Directory.

You will get some info about the connector and some statistics.

Under Connect Azure Active Directory logs to Azure Sentinel, Click on Connect on the Sign-ins logs and the Audit logs. That’s it to start collecting logs. It usually takes a couple of minutes for the logs to show up in Sentinel but ones that’s in place they update almost in real-time.
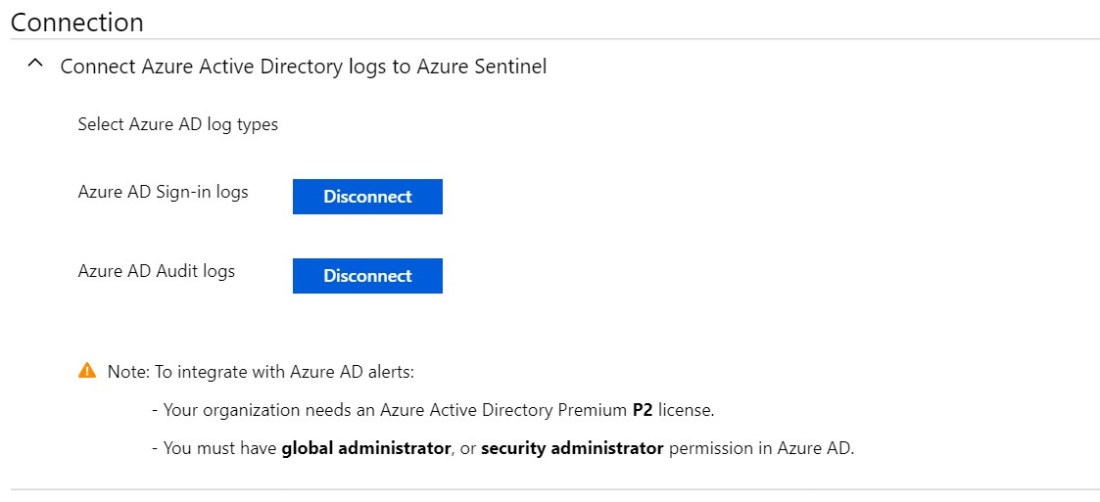
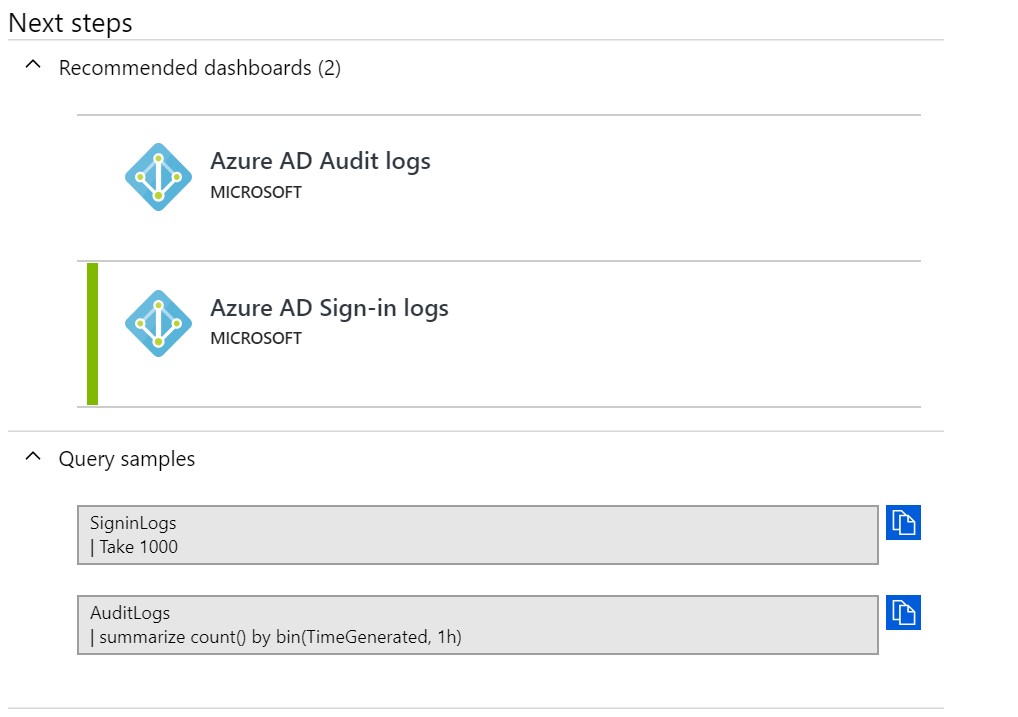
Also, install the dashboards under Recommended dashboards to get a nice view of the Azure AD logs. Most connectors have native dashboards that you can install for free.
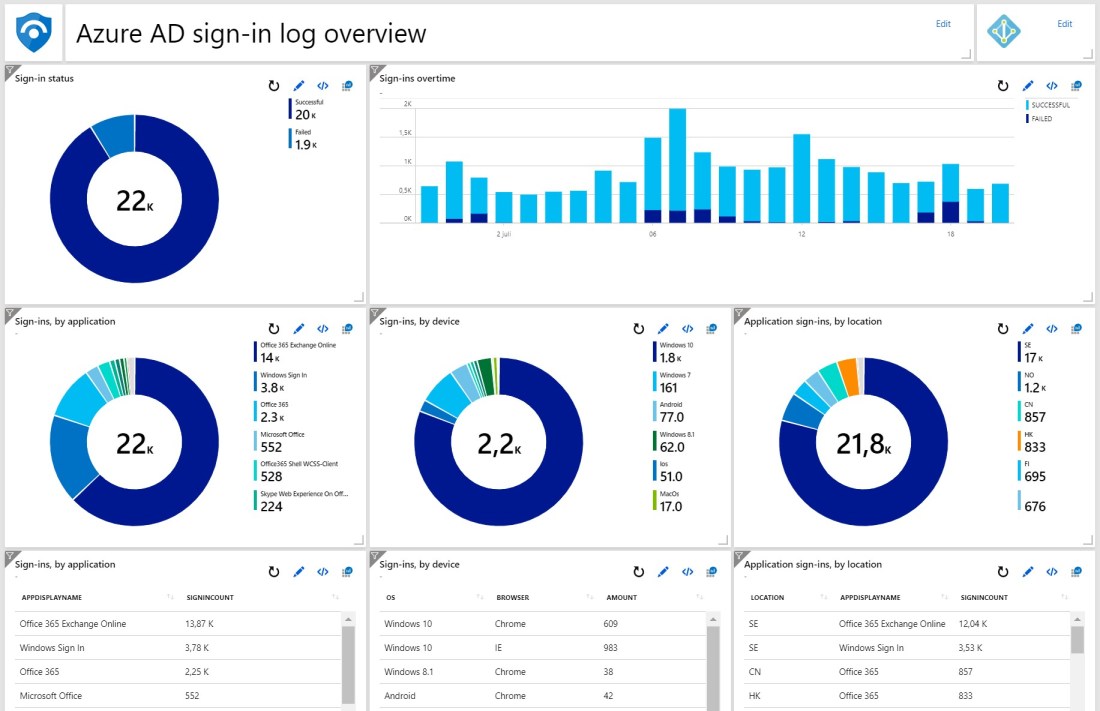
And this is how it will look in the Azure Portal dashboards section when you click on Azure AD Sign-ins.
Of course, this is just a quick guide for you to get started with Microsoft 365 log management in Azure Sentinel. The next step is to customize your dashboards and create alert rules when something looks out of the ordinary.
Summary
I hope this will get you started with Microsoft 365 monitoring in Azure Sentinel.
Since this is a very powerful tool and there seams to be a need for it out there I will put some energy into building some cool dashboards in the coming months. I will share my progress in upcoming posts. But for now, I’m heading back to my hammock.
More info about Sentinel here.
Please follow me here, on LinkedIn and on Twitter!